It took us a while. But we managed to do it. So, it's feasable!
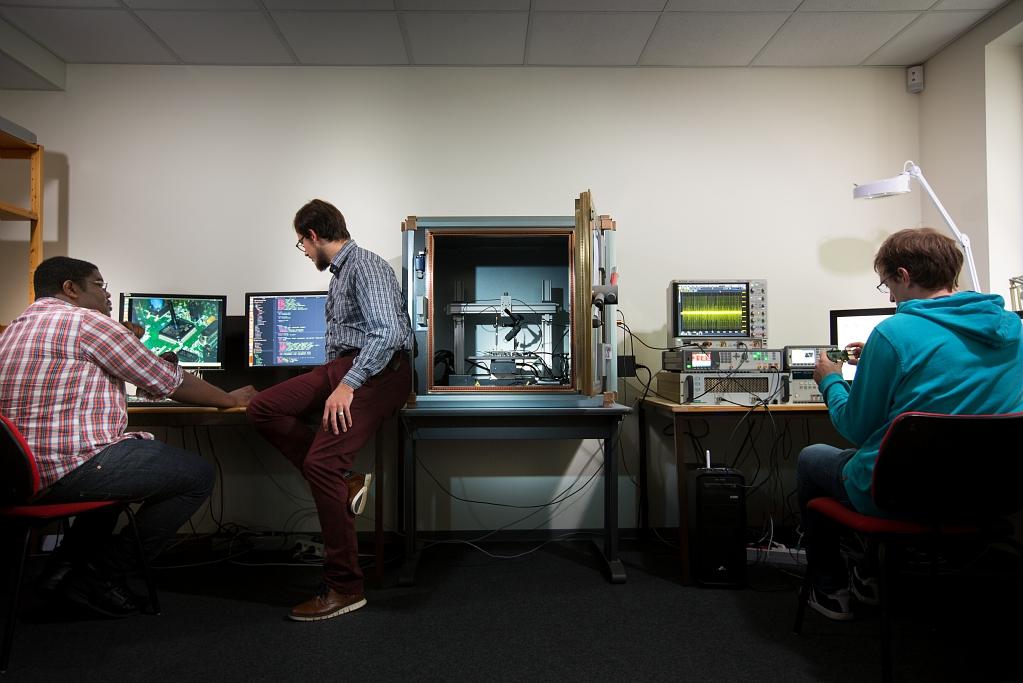
Ronan Lashermes is a research engineer at the High Security Lab (LHS) on Rennes science campus, a lab created by the French Defense Agency, Brittany Region, CentraleSupelec, CNRS and Inria, and available to digital security research teams and their industrial partners.
For four years, Ronan has been studying Electromagnetic Fault Injection attacks against hardware circuits.
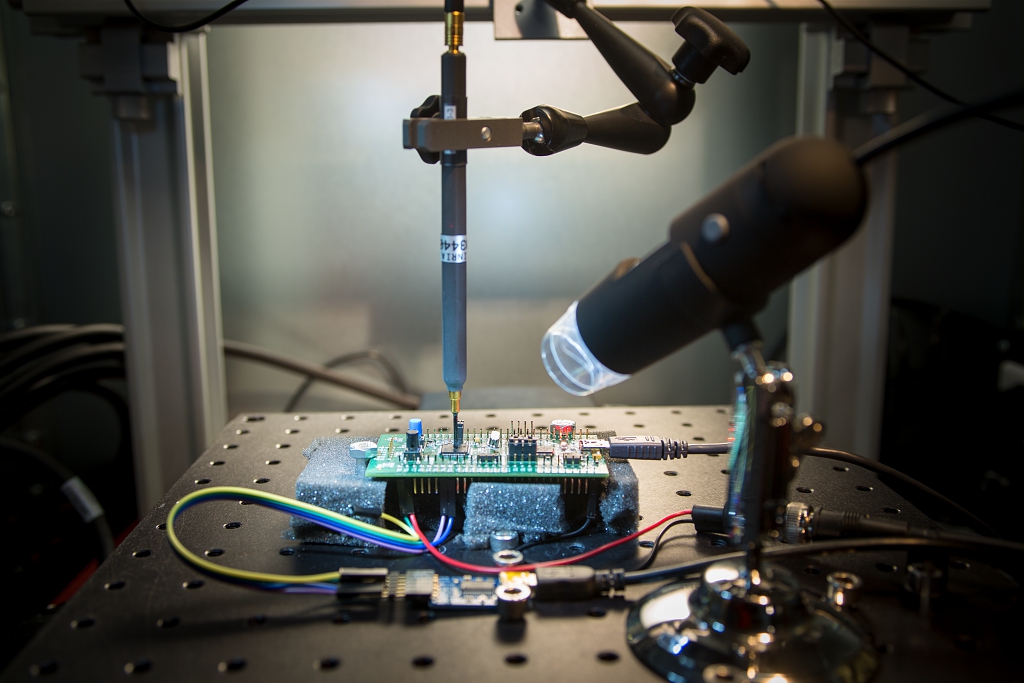
We use pulse generators. It's all a matter of fine tuning. Too weak a pulse, nothing happens. Too strong a pulse, the chip crashes. But in between, there is a narrow zone through which we can modify the chip's behavior in order to inject faults into the software being executed.
The first step of this scientific undertaking consists in “trying to get a better grasp of what signal should be emitted in order to obtain the desired behavior. In other words: how to run an efficient attack.” The goal here is to study the effects of impulses on the chip from a hardware point of view. This part of the work was assigned to Ludovic Chaudepierre whose post-doctorate is shared by the Institute of Electronics and Telecommunications of Rennes (IETR) and Cidre, a research team specializing in digital security (and common with Inria, CentraleSupelec, University of Rennes 1 and CNRS).
Securing Phones
“Historically, Lashermes points out, this kind of attack mostly targeted cryptography. It was used against payment cards in particular. But these are well protected nowadays. What got us interested in this field is the fact that transactions are now migrating toward smartphones which happen to have a lower level of protection against EMFI threats. From this point of view, the world has taken a step backward. And the risk extends beyond cryptography as chips end up doing a lot of other things these days, handling pin code for instance. Be that as it may, taking control of a telephone is still a matter that regards security. The Internet of Things is also a concern in this context.”
The scientists didn't just attempt to defeat the simplest circuits. “In the Cidre research team, we have a PhD work meant to target complex chips and study how faults can impact micro-architectures.” Carried out by Sebanjila Kevin Bukasa, directed by LHS Director Jean-Louis Lanet and advised by Lashermes, this thesis is financed by a world leader in digital security. The research is performed in partnership with the French cybersecurity agency (ANSSI). “At one point, it dawned on us that we had both started the same experiments separately.”
Major Implications for Chip Manufacturers
Complex chips are very different in terms of speed, of number of transistors, etc. Until now, nobody had being able to prove that they could fall prey to an EMFI assault. “But that's not the case anymore for we've just demonstrated that it could be done.” These findings are bound to have profound consequences for the industry, in particular for phone chip manufacturers.
Security wise, one must deeply rethink the way information runs on these chips. They are made of components that communicate through a network. Yet, this network isn't protected. An EMFI attack can thus access the information transiting on it. One must therefore secure this network. And that's our message.