The new challenges of network security
Date:
Changed on 07/12/2023
Fifty years ago, network security wasn't really an issue. Technical prowess lay in the ability to interconnect a few remote machines and make them communicate by exchanging data packets. There are now more than 4 billion users around the world and a great diversity of uses, particularly with the deployment of mobile terminals and connected devices. Cybersecurity is therefore a crucial challenge these days.
Isabelle Chrisment
The Internet has in fact become a playing field for cyberattacks, from the theft of personal data (credit card numbers, passwords, etc.) to the undermining of companies and even countries (ransomware, denial of service, etc.).
Hence the need these days to think about security right from the design stage of hardware and software, known as “security by design”. However, it remains fallible and it’s essential to update systems, software and hardware regularly to guarantee their security. In the case of connected devices, this must be easily doable by the user, via their smartphone for example. But this process can also open breaches in security – even if it is perfectly designed from the outset.
Jérôme François
Furthermore, network security has become much more complicated as you now have to monitor networks whose operators or administrators are not necessarily the service or content providers, with the growing demand for security. In practice, to guarantee cybersecurity, monitoring requires capturing network traffic “blind”, without knowing exactly the content circulating on it or the information being exchanged. Despite all this, you have to be able to deduce its potential legitimacy.
First, you have to remember that encryption of Internet communications has considerably improved over the course of the last decade, and since 2013 in particular. There is a lot more caution, especially since the Snowden affair which highlighted the possibility of third parties monitoring and collecting user data on a large scale, without their approval. However, although encryption clearly represents an advance for personal data protection, it creates new challenges for monitoring networks and for putting in place security mechanisms such as flow filtering and flaw detection.
Isabelle Chrisment
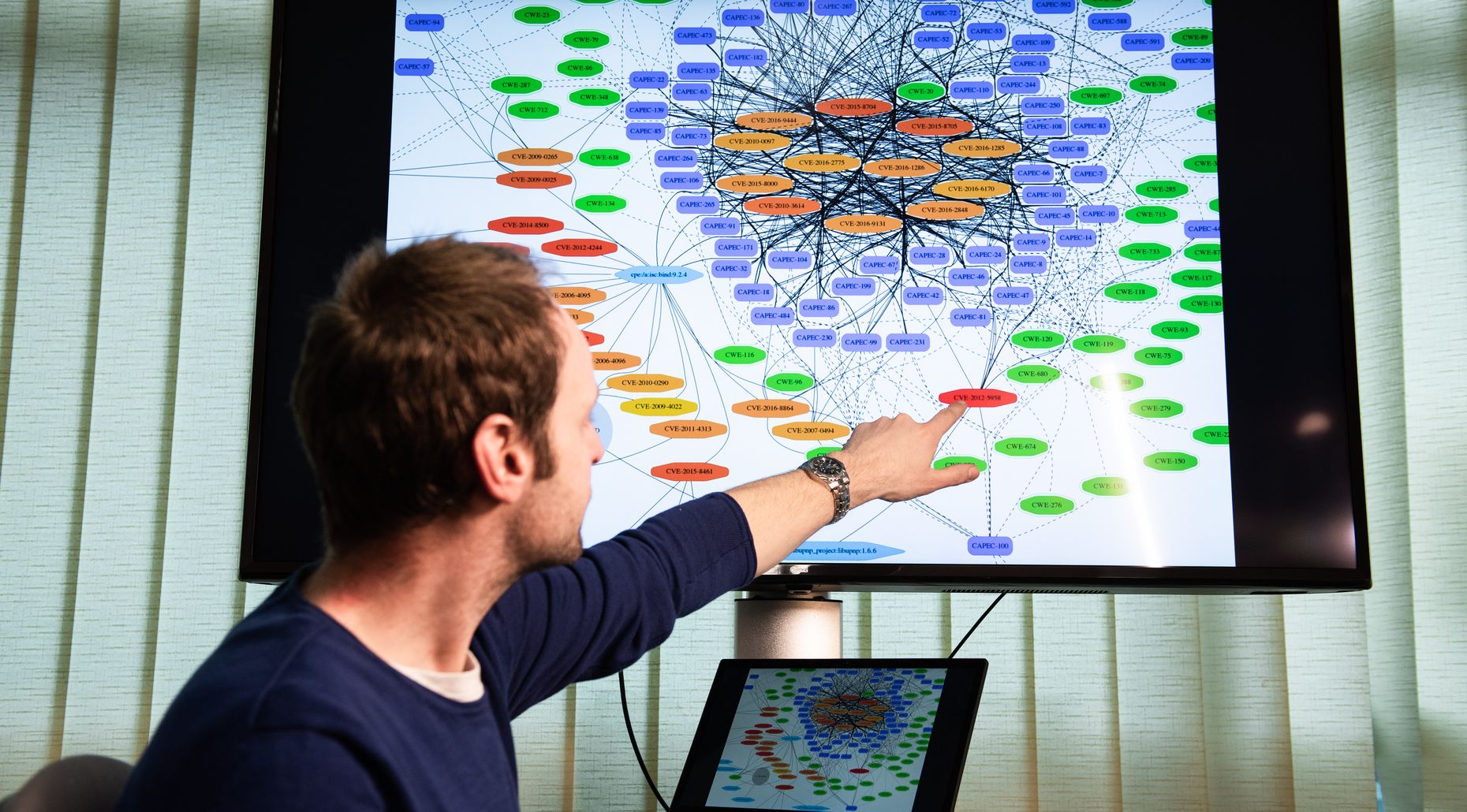
Our team focuses on network analysis and the analysis of associated services, and is working in particular on analysis of encrypted traffic. In fact, although the majority of web traffic these days is encrypted for entirely legitimate personal data protection reasons, it is also necessary to detect malicious actions in that traffic, such as attacks and viruses. We're therefore developing methods that detect only malicious activities, without compromising the traffic – that is, without decrypting it. To do so, we can focus on the few pieces of non-encrypted data that are circulating or on the attacker's behaviour; in other words, on the Internet services they’re using and how they’re changing over time.
Jérôme François
Our team isn't working directly on this technology. However, 5G's ability to offer much faster throughput while being mobile highlights an interesting fact: the challenge is now the capacity to process the large amounts of data that will be circulating.
Isabelle Chrisment
Operators such as access providers have a network infrastructure... However, they're not necessarily the ones who use it, because it could be a virtual operator that will lease the network, for services produced by others such as making music or films available or cloud-based data storage. This poses major questions in terms of balance between network monitoring (to prevent intrusions for example) and data confidentiality.
Jérôme François
Inria is an internationally recognised institute in security matters as it innovates in multiple fields. In the field of cryptography, Inria is working on numerous encryption and digital signature systems, and contributes to international standardisation efforts via the NIST (National Institute of Standards and Technology).
Jérôme François
Inria also already offers encryption systems that can withstand the computing power of quantum processors!
We can also cite the monitoring of systems via data analysis for security, such as in the case of network traffic or via events logged by the system, and large-scale monitoring with sensors which Inria has at the High Security Laboratory. For these activities, artificial intelligence and big data activities already play an important role and could in future become paramount.
Another field involves formal methods for detecting flaws in protocols such as TLS (Transport Layer Security), a protocol that secures exchanges over the Internet and offers encryption improvements such as proven end-to-end security.
Also, electronic voting and personal data protection are of course very important for society as a whole. The introduction of the GDPR (General Data Protection Regulation) in May 2018 must go hand in hand with the implementation of technical solutions, a good number of which still need to be worked out.
There are many cybersecurity challenges and they're not isolated from each other. At Inria, there are numerous security-related lines of research. In future it will be necessary to tackle real scientific challenges such as those mentioned in the Inria White Paper on Cybersecurity, released in January 2019. We can cite, among other things, post-quantum cryptography, “homomorphic encryption” that allows computation on encrypted data, end-to-end proofing of encryption protocols, preventive as well as reactive system security, including for those who integrate connected devices, and the strengthening of privacy protection. You can't actually think about cybersecurity without having a holistic approach and tackling all potential flaws!
Isabelle Chrisment