Allow me to introduce myself. My name is Belenios
I came into the world in 2012. My name refers to one of my main ancestors: Helios, the electronic voting freeware designed in 2008 by a researcher at Harvard University in the USA. This name was derived from the god of the sun in Greek mythology. My name, meanwhile, is a cross between Helios and Belenos, the Gaulish sun god. As a software program, my role is to reassure voters and the organisers of electronic ballots that the secrecy of their votes will be fully respected. I also help ensure that all results are transparent and verifiable at any time.
My objective: to lead the fight against fraud
The software developed by private companies and which is used, for example, by certain associations or trade unions, has not been found to be sufficiently secure: voter secrecy is not 100% guaranteed and transparency is not up to scratch, particularly when you take the proprietary and closed nature of these systems into account. I, on the other hand, am an open source platform, meaning that my “open” code can be analysed by third party tellers. Once a vote has been cast, the result is encrypted using a public key on the voter’s computer, before being sent to a server and stored until the end of the process.
My technical specifications
In order to make these processes secure, my creators devised cryptographic protocols that could be applied to all data exchanged. The core principle of this is multiple-key encryption: encryption involves the use of a public key, with decryption involving the use of a private key shared by different authorities. What this means is that you have to be able to group together enough “fragments” of this key (3 out of 5, for example) in order to obtain and declare definitive results.
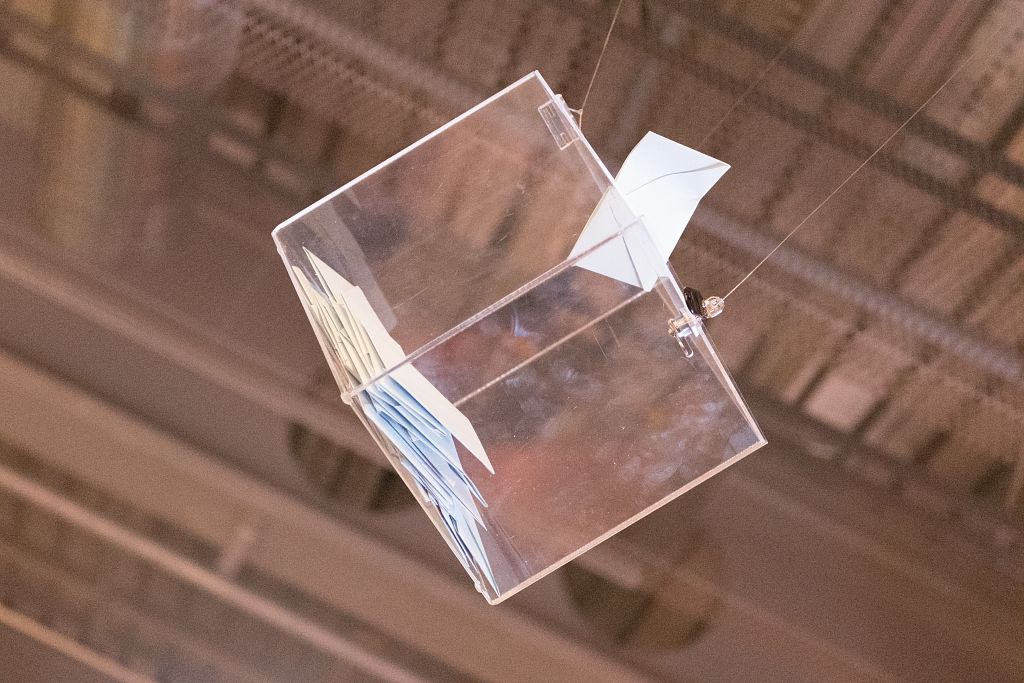
In much the same way, my system involves the allocation of an anonymous private key (comparable to a “right to vote”) to each voter: this key is specific to them and is never saved in the virtual ballot box, which only ever retains the public part of voters’ keys. “Voters can check to ensure that their ballot paper is in fact in the ballot box (individual verifiability)”, explains Véronique Cortier, a member of the Pesto project team. The wider community of voters, meanwhile, are able to ensure that the final result matches the votes cast (universal verifiability) by voters in possession of a key and a right to vote, rendering them eligible (eligibility verifiability).
My developers
I was designed by two project teams, both of which are joint undertakings involving Inria and Loria: Pesto (security protocols, particularly for electronic voting) and Caramba (cryptography and cryptanalysis). More specifically, I was co-created by the researcher Véronique Cortier (Pesto), the researcher Pierrick Gaudry (Caramba) and the research engineer Stéphane Glondu, who took care of the platform development side of things.
My upcoming challenges
My open source system, a showcase for the research that went into my creation, can be used for free by all organisations looking to ballot fewer than 1,000 voters: it has already been used by many academic institutions, for national committee elections and by certain companies and associations. I’m a bit bashful about this, but I have a keen interest in bodies responsible for organising electronic ballots on behalf of major institutions, such as Docaposte.
From a technical perspective, the team is still hoping to enhance the security of my system, helping me to become independent from the servers used and to ensure that my protocol is able to protect votes against any changes, even if the voter’s computer cannot be trusted (i.e. if it has been corrupted). The team is also hoping to develop a system capable of resisting any attempts at buying votes and to ensure that it can be used to organise more complex ballots (ranking candidates in order of preference, for example).