SCUBA: automated audits for connected objects
Date:
Changed on 07/12/2023
I was born in early 2018 in Nancy to help identify security threats for “new” connected objects. These devices - thermostats, voice assistants, switches, internet boxes, gas meters, lighting systems, video surveillance systems, etc. - are increasingly common, both in people’s homes and in businesses. “Very often, however, they have either very little security or none at all”, comments Abdelkader Lahmadi, a research professor at the University of Lorraine and member of the RESIST team, a joint undertaking involving Inria and Loria. “The main reason for this is that manufacturers have to keep the resources needed for these appliances (processing capacity, memory, storage, etc.) to a minimum: they need to be cheap and to use relatively little energy.”
Connected objects are, by definition, connected to the internet, where they seamlessly share private information with standard applications or online services. They are also capable of receiving information, which allows them to function remotely, for example. The rise in the popularity of these objects has seen an increase in the number of attacks attempting to exploit certain weak points, the goal being to divert these devices from their primary functions and to involve them in coordinated, large-scale attacks. This was the case a number of years ago, when hundreds of thousands of connected objects were infected by a malware called Mirai. The contaminated devices were diverted in order to bombard France’s main web hosting service (OVH), to such an extent that it was no longer able to function properly (a “distributed denial of service” or DDoS attack).
I am made up of a software suite supplying audit and diagnostic tools to three main categories of users: individuals (who may be informed of the security level of their object via a label), manufacturers (some of whom already use SCUBA to identify potential weaknesses in their products and to rectify them) and major security specialists (who use SCUBA to gauge the reliability of the devices used by their clients).
I use artificial intelligence, in particular new machine learning algorithms combining symbolic and statistical learning technology. I was designed to automatically evaluate the security of connected objects with as little human involvement as possible and in near real time.
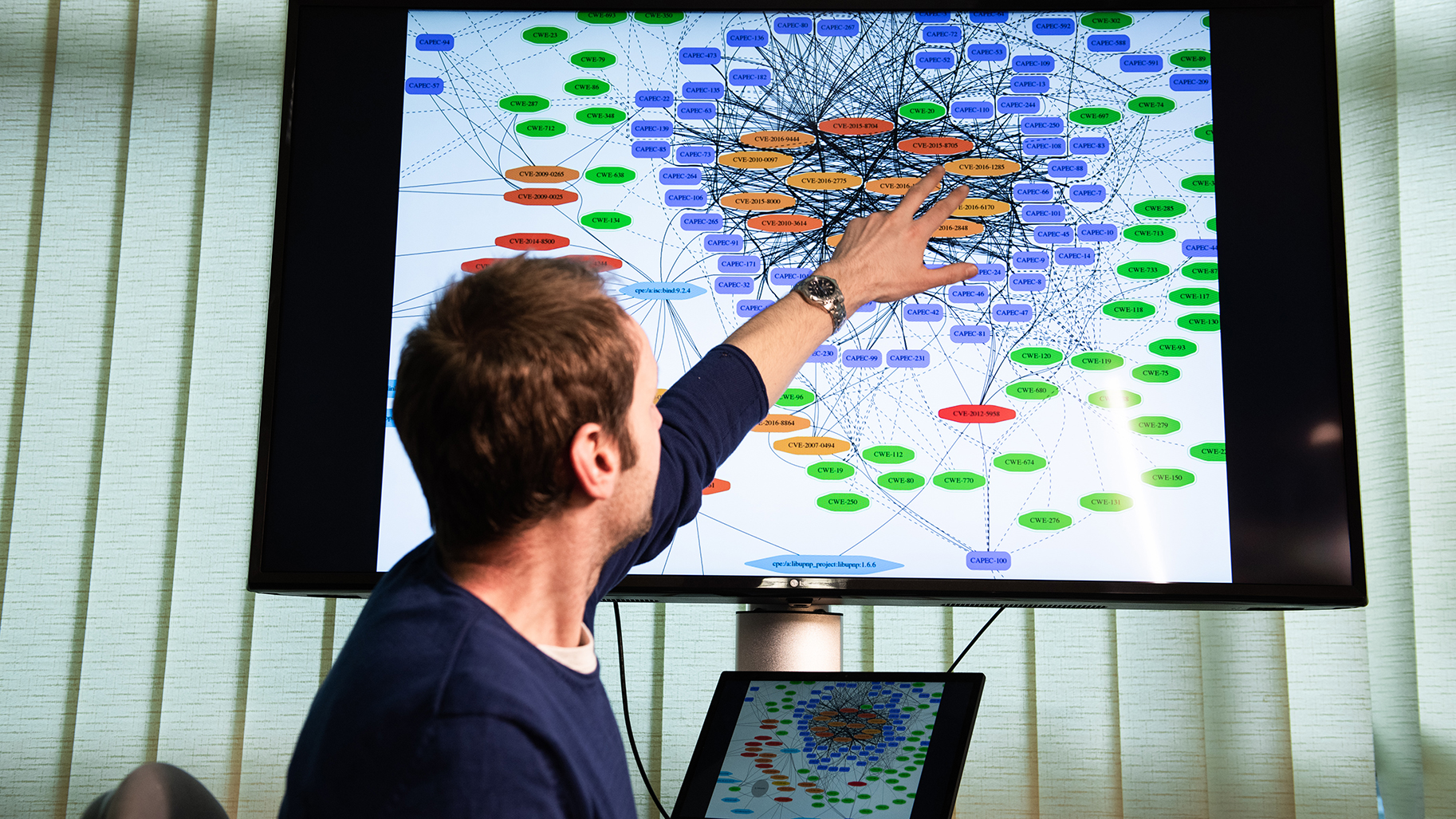
“What makes the SCUBA platform original is that it can be used to carry out a security audit on an object in its wider environment, not just in isolation”, explains Frédéric Beck, one of my creators, who is also an engineer and technical manager at the Inria Nancy Grand Est research centre’s high-security laboratory. “We focus on how the connected object interacts with everything else around it” (a connected light bulb is not subject to the same environment nor the same risks if it is directly plugged into a socket or to a switch that is also connected). The tool automatically compiles “knowledge graphs” featuring potential links to other components whose vulnerability is already known.
I was developed by the RESIST research team, which deals with security and the monitoring of large networks of systems. Particularly key to my development was the cybersecurity expertise of Abelkader Lahmadi and Jérôme François, an Inria research fellow, Frédéric Beck’s research into network protocols and developments by Thomas Lacour, an Inria engineer.
One of the biggest issues I have to deal with is the diversity of the communication protocols used by communicating objects: there is no common standard, with almost as many communication protocols as categories of equipment to take into account (cameras and thermostats, for example, use different protocols). I also have to tackle the complexity of the required machine learning algorithms: these have to be capable of processing vast deposits of miscellaneous, non-structured data generated by machines.
Finally, my creators, on the back of the interest my development has generated in the industrial sphere, are looking into the possibility of launching a start-up and patenting some of their inventions. It might not be long before I’m marketed to manufacturers of objects and security companies.